Med USA
Revenue Cycle Management, Credentialing, and Real-Time Analytics.
YOUR REVENUE CYCLE:
OPTIMIZED
"In my tenure, I hold building a partnership with Med USA as one of my greatest accomplishments!"
Scalable Solutions Whether You Operate a Small Practice or a Large Provider Health System
Orthopaedic Surgery Billing
Urgent Care Billing
Behavioral Health Billing
Medical Billing
Healthcare Analytics
Revenue Cycle Administrator
Compliance Experts
REAL-TIME
Healthcare Analytics
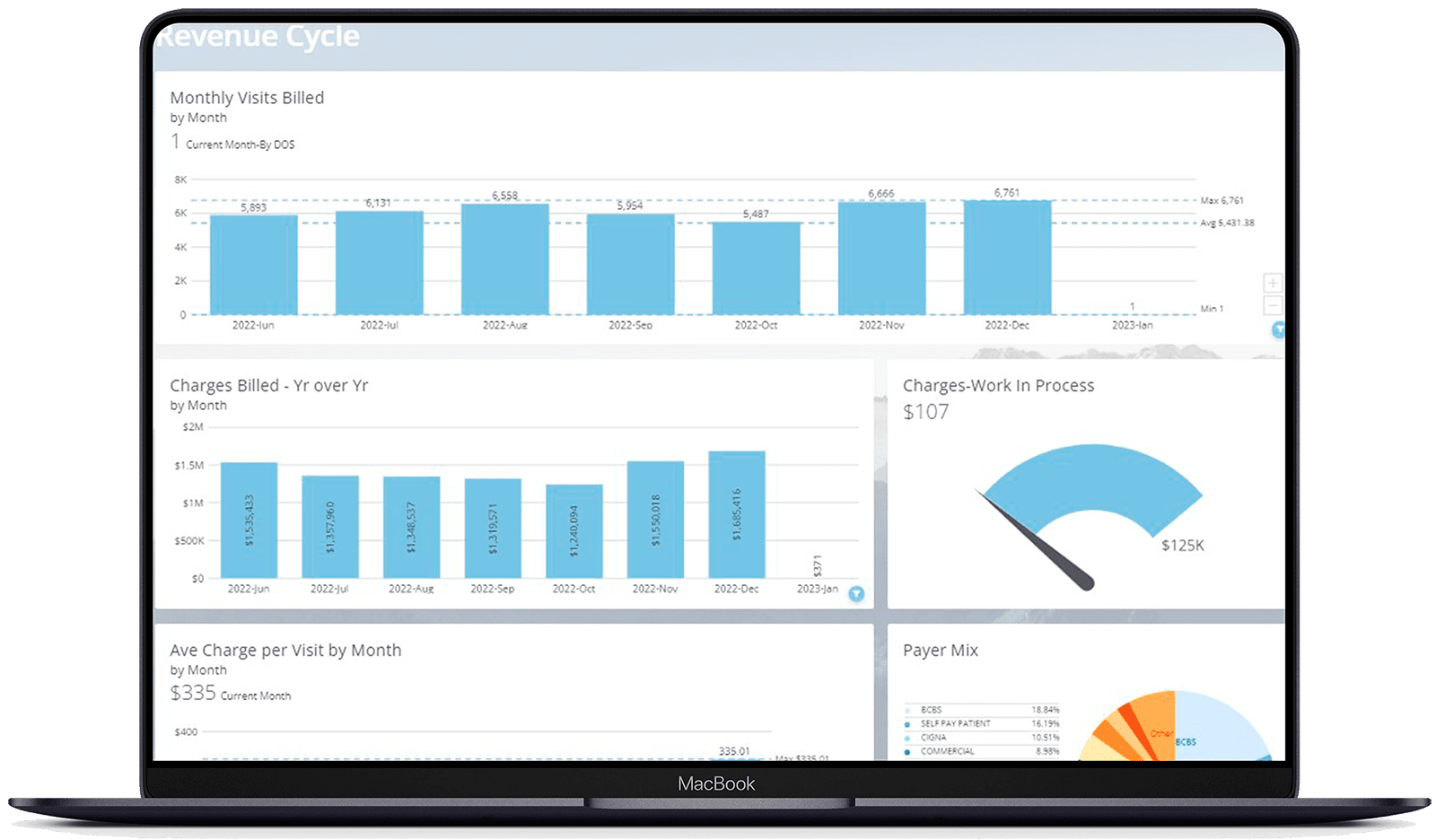
Med USA provides in-depth, ad hoc analytics tools powered by Domo that give you full transparency into the health of your practice or multi-location healthcare group. Our reports help providers and administrators report benchmarks, revenue, relative value units, outcomes, and forecast easily in real time. We bring all your practice’s scattered data sources into one simple, easy-to-use platform.
Testimonials
Professionals like you are talking about Med USA

Reach out to see how our team can help!
Optimize Your Practice Today
Turn to the expert Med USA team when you need customized and adaptable solutions for all the services that make running your practice easier:
- Revenue Cycle Management
- Provider Credentialing
- Healthcare Compliance
- Healthcare RCM Analytics
How much revenue is your practice missing?